Bootstrap Token Deployment
Automate Pult Agent enrollment using bootstrap tokens -- no manual sign-in required.
Bootstrapping lets you link a Pult Agent installation to a user account without requiring the employee to sign in manually. A bootstrap token -- generated in the Pult Dashboard -- is deployed to the device so the agent can automatically initiate enrollment.
How It Works
- An admin generates a bootstrap token in the Pult Dashboard.
- The token is deployed to the device via one of the supported methods (CLI, MSI property, or file).
- The agent reads the token and initiates a Device Auth Request, sending basic device information (device name, OS, serial number).
- The request appears under Settings → Presence → Device Authentication → Pending Requests.
- An admin reviews and approves the request, matching it to a Pult user.
- The agent receives an access token and the device is fully enrolled.
If you have an MDM integrated, Pult can automatically suggest the matching user by looking up the device's serial number in the MDM inventory. An admin still needs to explicitly approve the request.
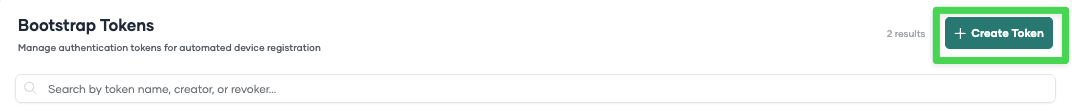
Creating a Bootstrap Token
- In the Pult Dashboard, go to Settings → Presence → Device Authentication.
- In the Bootstrap Tokens section, click Create Token.
- Enter a name (e.g., "Q1 2026 Rollout") and set an expiration date.
- Click Create. The token is displayed once -- copy it immediately and store it securely.
Token Lifecycle
- Active -- The token is valid and can be used for new enrollments.
- Expired -- The token has passed its expiration date and can no longer be used.
- Revoked -- The token was manually revoked by an admin.
You can view and manage all tokens in the Bootstrap Tokens table on the Device Authentication page.
Deploying the Token
Three delivery methods are available. Choose based on your deployment infrastructure.
Method 1: Command-Line Flag
Run the agent binary with the --bootstrap-token flag. This writes the token to secure storage and
exits immediately -- it does not start the agent.
macOS:
"/Applications/Pult Agent.app/Contents/MacOS/pult-agent" --bootstrap-token "your-token-here"Windows:
"C:\Program Files\Pult Agent\pult-agent.exe" --bootstrap-token "your-token-here"This command requires an active, interactive user session. It accesses the user's keychain/credential store, which is only available when the user is signed in to the OS.
Method 2: MSI Property (Windows Only)
Pass the token as an MSI installer property during installation:
msiexec /i pult-agent.msi BOOTSTRAP_TOKEN="your-token-here" AUTOLAUNCHAPP=1| Property | Default | Description |
|---|---|---|
BOOTSTRAP_TOKEN | (none) | Sets the bootstrap token during installation |
AUTOLAUNCHAPP | 0 | Set to 1 to launch the agent immediately after install |
AUTOSTART_ALLUSERS | 1 | Auto-start the agent at user login (enabled by default) |
MSI properties require the installer to run in user context. Some MDMs (e.g., Microsoft Intune) run installers in SYSTEM context, which breaks these properties. For Intune, use the Intune deployment guide instead.
Method 3: File-Based Deployment
Place a plain-text file containing the token in a specific directory. The agent watches these directories and automatically picks up the token.
Valid file names (case-insensitive): BOOTSTRAP_TOKEN, BOOTSTRAP-TOKEN, BOOTSTRAP-TOKEN.txt
File locations:
| Platform | Directories (searched in order) |
|---|---|
| Windows | %PROGRAMDATA%\com.pult.agent\ then %APPDATA%\com.pult.agent\ |
| macOS | ~/Library/Application Support/com.pult.agent/ |
The file should contain only the token text (no formatting, no newlines). After the agent reads the token:
- The token is transferred to secure storage (Keychain / Credential Manager).
- The token file is automatically deleted.
This method works well when:
- Your MDM runs installers in SYSTEM context (where MSI properties don't work).
- You need to separate app installation from token provisioning.
- You want a cross-platform approach that works identically on Windows and macOS.
Token Format
Bootstrap tokens must be:
- 1--128 characters long
- Alphanumeric characters, hyphens (
-), and underscores (_) only
Updating a Token on an Already-Installed Agent
If the agent is already running, you can update the bootstrap token:
Using CLI (set + reload):
pult-agent --bootstrap-token "new-token-here"
pult-agent --reload-bootstrap-tokenUsing file-based method: Write the new token to the file location. The running agent detects and consumes it automatically.
Security Considerations
- Tokens are stored in the OS secure storage (macOS Keychain / Windows Credential Manager) after consumption.
- File-based tokens are stored in plain text temporarily on disk. The agent deletes the file after reading. Use short-lived tokens when using this method.
- Token validity is enforced server-side -- expired or revoked tokens are rejected.
- Always verify Device Auth Requests by checking the request timing and IP address before approving. See Device Authentication.
Last updated on Apr 20, 2026, 10:32 PM